Operational resilience is often reduced to disaster recovery.
Backups.
Failover systems.
Incident response plans.
These are important. But they address only part of the problem. Modern systems are not defined by how quickly they recover from failure. They are defined by how well they continue operating during failure. That distinction changes how resilient systems must be designed.
Resilience is a system property
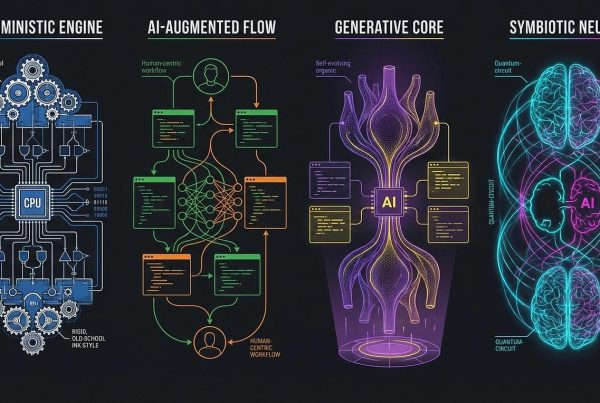
Traditional systems are designed around recovery.
Detect failure.
Restore services.
Return to normal operation.
Resilient systems are designed differently.
They anticipate disruption.
Contain operational impact.
Maintain critical functionality under degraded conditions.
The objective is no longer:
“How quickly can we recover?”
But:
“How much disruption can the system absorb while remaining operational?”
Modern systems operate under constant dependency
Most systems no longer operate independently. They depend on:
- cloud infrastructure
- APIs
- third-party services
- external platforms
- distributed workflows
Each dependency introduces uncertainty. When systems are tightly coupled, local failures become system-wide failures. Resilient systems are designed with this uncertainty as a structural assumption.
Resilience must be designed into the architecture
Operational resilience cannot be added later. It affects:
- system boundaries
- data ownership
- workflow execution
- dependency management
- operational state consistency
Well-designed systems isolate failure instead of propagating it. This allows disruption to remain controlled rather than cascading across the system.
Fragile systems only work under ideal conditions
Many systems appear stable until operational pressure increases. Growth introduces:
- higher load
- additional dependencies
- increased workflow complexity
- more integration points
Without structure, systems become unpredictable under stress.
Failures spread more easily.
Recovery becomes slower.
Operational coordination increases.
The system becomes fragile.
Resilient systems prioritise continuity
Operational resilience is fundamentally about continuity. This means systems must:
- maintain critical workflows
- preserve data integrity
- operate predictably under degradation
- continue functioning during partial failure
Resilience is not binary. Systems do not move simply between “working” and “broken.” Good systems degrade gracefully while remaining operationally controlled.
Observability enables operational control
Resilient systems require visibility into how they behave. Without observability:
- failures remain opaque
- dependencies become unclear
- operational decisions become reactive
Well-structured systems maintain continuous visibility into:
- operational state
- workflow execution
- system dependencies
- failure propagation
This allows systems to remain manageable under pressure.
Resilience and scalability are connected
Systems that become less predictable as they grow are not truly scalable. Scalable systems maintain:
- operational consistency
- controlled dependencies
- predictable behaviour
- maintainable architecture
Complexity increases. But it remains contained.
Final perspective
Operational resilience is not fundamentally about recovery. It is about maintaining control under disruption. The difference between fragile systems and resilient systems is rarely infrastructure alone. It is architecture. Because resilient systems are not designed only to function under ideal conditions. They are designed to remain operational when conditions are no longer ideal.
Resilient systems are not defined by how they recover.
They are defined by how they continue operating under failure.
If your systems become less predictable as complexity increases, the architecture behind them may need to change.