Cybersecurity is still often treated as a final step in software development.
A penetration test before release.
A checklist before deployment.
That approach no longer works. Modern systems operate continuously across:
- APIs
- cloud infrastructure
- distributed services
- external integrations
Security can no longer be validated at the end. It must be designed into how systems operate from the beginning.
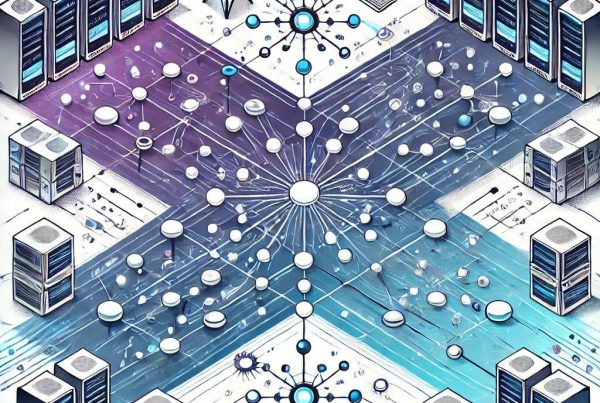
Security is a system property
Secure systems are architecturally different systems. Security is not an additional layer. It affects:
- how systems communicate
- how data flows
- how permissions are enforced
- how failures are contained
The question is no longer:
“Is this secure?”
But:
“Is this system structured to remain controlled under failure, misuse, and attack?”
Security must exist inside development workflows
In modern engineering environments, security cannot operate separately from development. It must be embedded continuously into:
- development pipelines
- deployment workflows
- testing environments
- operational monitoring
This allows vulnerabilities and structural weaknesses to be identified before systems become operationally exposed.
Weak system structure creates security risk
Security failures are often structural failures. Systems become vulnerable when:
- integrations are loosely controlled
- permissions are inconsistent
- data flows are unclear
- dependencies are unmanaged
- operational logic becomes fragmented
At that point, security becomes reactive. Teams patch symptoms instead of improving system integrity.
Secure systems assume complexity
Modern systems are highly interconnected. Applications depend on:
- external services
- third-party dependencies
- distributed infrastructure
- continuous deployment
This increases operational exposure. Secure systems are designed with the assumption that:
- failures will occur
- systems will evolve
- dependencies will change
- attack surfaces will expand
Architecture determines whether systems remain resilient as complexity increases.
Security and operational resilience are connected
Security is not only about preventing attacks. It is about maintaining control during failure conditions. Well-designed systems:
- isolate failures
- enforce boundaries
- reduce dependency risk
- maintain observability
- recover predictably
Security becomes part of operational behaviour itself.
Automation and security must operate together
As systems scale, security cannot rely on manual enforcement. Secure systems require:
- continuous validation
- repeatable controls
- observable workflows
- automated verification
Without this, security becomes dependent on operational coordination. And coordination does not scale reliably.
Good systems remain secure by design
Well-designed systems:
- reduce unnecessary exposure
- isolate operational risk
- enforce consistency structurally
- remain maintainable as they evolve
Security is not added later. It is embedded into how the system behaves.
Final perspective
Cybersecurity is often treated as protection. But in modern systems, security is fundamentally about structure. The difference between systems that continuously accumulate vulnerabilities and systems that remain resilient under complexity is rarely tooling alone.
It is architecture.
Secure systems are not created through final checks.
They are created through structural design.
If security only becomes a concern after development, the system architecture is already working against you.