Cybersecurity is still often treated as a final step in software development.
A penetration test before release.
A checklist before deployment.
That approach no longer holds.
In modern systems, security cannot be validated at the end.
👉 It must be designed, built, and enforced continuously.
This shift is commonly referred to as DevSecOps.
But in practice, it goes further.
In a software engineering studio, security is not a separate function.
👉 It is part of how software is designed, developed, and maintained from day one.
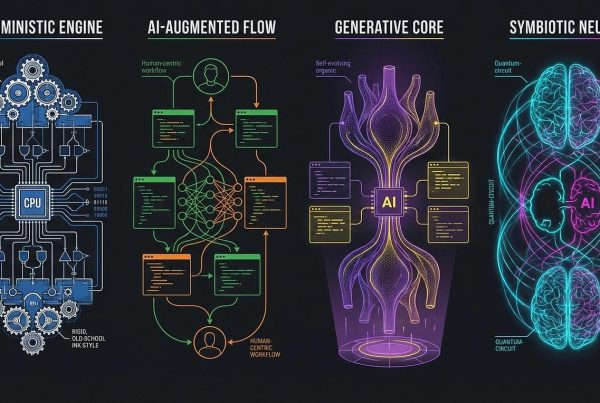
🧠 The Shift: From Security Checks to Security Systems
Traditional approach:
- build features
- test functionality
- add security checks
Modern approach:
- design for security
- enforce security during development
- validate continuously
This introduces a different mindset.
Not:
👉 “Is this secure?”
But:
👉 “Is this system structured in a way that prevents failure and misuse?”
⚙️ Security as Part of the Development Workflow
Security-as-Code
Security must be embedded into the development pipeline.
This includes:
- automated vulnerability scanning (SAST, DAST)
- security checks integrated into CI/CD pipelines
- real-time feedback in developer environments
This ensures that vulnerabilities are detected:
👉 during development—not after release
Proactive Threat Modeling
Security is not only about fixing vulnerabilities—it’s about anticipating them.
Before implementation, teams should:
- map system interactions
- define data flows
- identify potential attack vectors
Frameworks such as STRIDE provide structure for this process:
- Spoofing
- Tampering
- Repudiation
- Information Disclosure
- Denial of Service
- Elevation of Privilege
👉 The goal is to design systems that are secure before they are built.
Automated Security Testing
Manual testing is not sufficient at scale.
Secure systems rely on:
- static analysis (SAST)
- dynamic analysis (DAST)
- dependency scanning
These processes must be:
- automated
- repeatable
- integrated into development
🧩 Core Engineering Practices
Secure Coding Standards
Security starts at the code level.
Developers must follow established standards such as:
- OWASP Top 10
- SEI CERT
These define common failure points:
- injection vulnerabilities
- broken authentication
- insecure data handling
Input Validation
All input should be treated as untrusted.
This includes:
- user input
- API requests
- third-party data
Systems must validate:
- format
- type
- intent
Without validation:
👉 systems execute assumptions instead of logic
Secrets Management
Sensitive data must never be exposed.
Secure systems:
- avoid hardcoding credentials
- use dedicated secret management solutions
- enforce access control
Examples include managed services such as AWS Secrets Manager or HashiCorp Vault.
Dependency and Supply Chain Security
Modern software relies heavily on external libraries.
Each dependency introduces risk.
Secure systems:
- track dependencies
- scan for vulnerabilities
- update regularly
This reduces exposure to supply chain attacks.
🧠 The Studio Model: Culture and Collaboration
In a software engineering studio, security is not owned by a single team.
It is:
👉 shared responsibility
This requires:
- developers who understand security implications
- peer reviews focused on security, not just functionality
- continuous knowledge sharing
Security becomes part of:
👉 how teams think—not just what they do
🔄 Integrating Security into Daily Work
Peer Review and Pair Programming
Security should be part of:
- code reviews
- collaborative development
Not as an afterthought, but as a standard.
Continuous Learning
Threat landscapes evolve rapidly.
Modern teams must stay updated on:
- new attack vectors
- evolving vulnerabilities
- emerging technologies (e.g. AI-generated code risks)
Monitoring and Feedback Loops
Security does not stop at deployment.
Systems must:
- detect anomalies
- monitor behavior
- respond to threats
🧠 Emerging Trends (2026 and Beyond)
AI-Native Development Risks
AI-assisted coding increases speed—but also introduces:
- unverified code
- hidden vulnerabilities
This requires:
👉 stronger validation and auditing
Zero Trust Architecture
Modern systems assume:
👉 breach is possible
This leads to:
- strict identity verification
- least-privilege access
- continuous authentication
Software Supply Chain Security
Tracking all components of a system becomes essential.
This includes:
- Software Bill of Materials (SBOM)
- dependency transparency
- vulnerability tracking
📈 What Secure-by-Design Systems Achieve
A secure system:
- reduces attack surface
- prevents common vulnerabilities
- isolates breaches
- protects critical data
- scales without increasing risk
Security does not eliminate threats.
👉 It ensures systems remain controlled under them.
🚀 Final Thought
Cybersecurity is often treated as protection.
But in modern systems, it is:
👉 structure
The difference between a system that is continuously patched
and one that is fundamentally secure
…is not tooling.
👉 It is how the system is designed.
If security becomes a concern only after development, the system is already at risk.
We design and build software where security is embedded from the start—across architecture, development, and operations.






Recent Comments